Internet Secure Tunneling 2.0.0.244
Free Trial Version
Publisher Description
Internet Secure Tunneling can forward otherwise insecure TCP traffic through encrypted SSH Secure Shell tunnel. You can secure for example DATABASE, POP3, SMTP and HTTP connections that would otherwise be insecure.
The tunneling capability of SSH Secure Shell is a feature that allows, for example, company employees to access their email, company intraweb pages and shared files securely by even when working from home or on the road.
Tunneling makes it possible to access email from any type of Internet service (whether accessed via modem, a DSL line or a cable connection, or a hotel Internet service). As long as the user has an IP connection to the Internet she can get her mail and access other resources from anywhere in the world securely.
This often is not the case with more traditional IPSec based VPN technologies because of issues with traversing networks that are implementing Network Address Translation (NAT) - this is especially the case in hotels. NAT breaks an IPSec connection unless special protocols such as NAT-Traversal are implemented on the client and gateway.
The client-server applications using the tunnel will carry out their own authentication procedures, if any, the same way they would without the encrypted tunnel.
The protocol/application might only be able to connect to a fixed port number ( e.g. IMAP 143). Otherwise any available port can be chosen for port forwarding.
Features
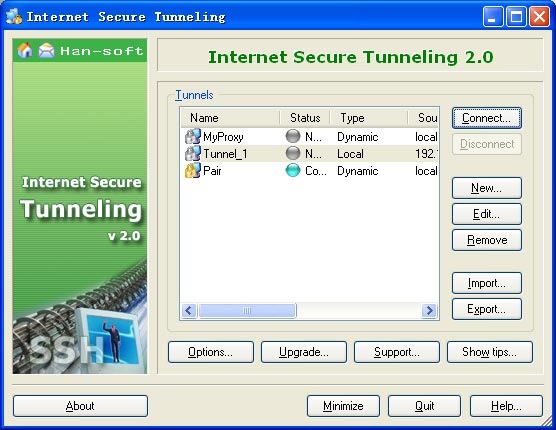
- Create and manage mulitiple SSH tunnels.
- SSH Version 1 and Version 2 are supported.
- Comperssion is supported.
- Remote forwarding, local forwarding and dynamic forwarding are supported.
- Hides in the system tray and does not require any desktop space.
- System tray pop up menu for easy access to main functions.
- Online support, online upgrade are supported.
- Windows XP compatible user interface.
About Internet Secure Tunneling
Internet Secure Tunneling is a free trial software published in the Encryption Tools list of programs, part of Security & Privacy.
This Encryption Tools program is available in English. It was last updated on 22 April, 2024. Internet Secure Tunneling is compatible with the following operating systems: Windows.
The company that develops Internet Secure Tunneling is Han-soft Software. The latest version released by its developer is 2.0.0.244. This version was rated by 6 users of our site and has an average rating of 4.2.
The download we have available for Internet Secure Tunneling has a file size of . Just click the green Download button above to start the downloading process. The program is listed on our website since 2006-05-29 and was downloaded 433 times. We have already checked if the download link is safe, however for your own protection we recommend that you scan the downloaded software with your antivirus. Your antivirus may detect the Internet Secure Tunneling as malware if the download link is broken.
How to install Internet Secure Tunneling on your Windows device:
- Click on the Download button on our website. This will start the download from the website of the developer.
- Once the Internet Secure Tunneling is downloaded click on it to start the setup process (assuming you are on a desktop computer).
- When the installation is finished you should be able to see and run the program.